Muqawama Cyber-Surge (Part 1): Chronology of Recent Attacks
Sabereen News appears to have added cyberattacks to its normal activities of spreading militia propaganda and disinformation, claiming operations against Israeli, Turkish, and Saudi targets.
A newly established Iraqi muqawama (resistance) facade group called "al-Tahirah Team” (spelled ALtahrea by the group itself) has claimed credit for a series of high-profile cyberattacks. The channel uses three green lizard icons in its posts and frequently adds the profane, half-capitalized English tagline “It Burns when I pee.”
Al-Tahirah (which means “pure” in Arabic) is a longstanding nickname for the major militia outlet Sabereen News, and the ties between the two entities are clear. Al-Tahirah Team’s Telegram channel was created on April 19, the same day the first cyberattack took place, yet Sabereen has referred to itself as “Sabereen al-Tahirah” and “al-Tahirah” since as far back as 2020. Moreover, Sabereen has worked closely with al-Tahirah Team during the past week, reposting its content and advertising its alleged capabilities. And on April 19, Sabereen referred to “Fariq al-Tahirah Sabereen Neyuz” in Arabic, meaning “the Tahirah Team of Sabereen News."
Israeli Targets (April 19-20)
On April 19, Sabereen posted the following warning: “At 1:02 [am] Qasem Soleimani and Abu Mahdi al-Muhandis time. The Zionist entity must prepare well.” The stated Baghdad time is the exact moment when Iranian general Soleimani and militia leader Muhandis were killed by an American strike on January 3, 2020. Sabereen’s message ended with the English sentence, “We ll never forgive, we ll never forget [sic]" (Figure 1).
Then, at exactly 1:02 hours Baghdad time, Sabereen posted that al-Tahirah Team was launching a cyberattack against the websites and servers of Israeli state media outlets (Figure 2). Confirmed as a distributed denial of service (DDoS) operation, the attack managed to take down the websites of KAN News and Channel 9 (a Russian-language television station in Israel) for a short period of time.
Afterward, al-Tahirah Team, Sabereen, and affiliated channels pledged to launch more attacks. On April 20, Sabereen posted a message with the number “21” and three green lizard icons, apparently as forewarning of further cyberattacks. At 21:00 hours Baghdad time, the website of the Israel Airports Authority was attacked and taken offline; it returned to service in a matter of minutes.
Turkish Targets (April 22)
On April 22, the same channels foreshadowed and then claimed similar cyberattacks on three Turkish websites: for the Presidency of Turkey, for the state-run news outlet Anadolu Agency, and for Baykar, the major defense company famous for manufacturing the Bayraktar drone series, which may have been used in recent weeks against muqawama targets. The cyberattacks took the websites offline for a short period, though they returned to service within minutes. As with the Israeli attacks, al-Tahirah Team (along with Sabereen and other muqawama media accounts) counted down to the attacks, posted the three lizard icons, and used the “It Burns when I pee” tagline.
Saudi Targets (April 23)
At 18:04 hours Baghdad time on April 23, another muqawama Telegram channel posted a simple graphic indicating that a cyberattack would occur at 21:00. This was subsequently echoed by Sabereen, while al-Tahirah Team posted an English-language statement indicating intent to launch further attacks and reiterating the 21:00 time (Figure 3). At 20:59 and 21:01, respectively, the channels announced cyberattacks on Saudi Arabia's General Authority of Civil Aviation and Ministry of Energy.
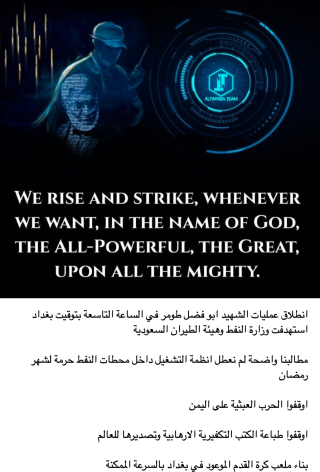
Al-Tahirah Team followed the operation with an Arabic post that tied the 21:00 attack to last year's killing of Yemeni Houthi soldier Abu Fadl Tomer. The channel also claimed that it had chosen not to disable the operating systems inside Saudi critical infrastructure out of respect for Ramadan. Yet all of the incidents in the multi-nation cyber campaign appear to have been DDoS website takedowns, so it is unclear whether the perpetrators actually have the ability to affect internal operating systems at this time.
In contrast to prior statements, al-Tahirah Team laid out several eclectic demands to Saudi Arabia: to stop the war in Yemen, to stop printing and exporting takfiri (apostate) books, and to build a promised football stadium in Baghdad (Figure 4). In 2018, King Salman had pledged to then-prime minister Haider al-Abadi that Riyadh would fund construction of a 135,000-person stadium in the city, so al-Tahira's latter demand was presumably intended as mockery for not fulfilling that promise.
Iraqi Media Targets (April 24)
At 23:19 and 23:35 hours, respectively, al-Tahirah Team announced cyberattacks on the websites of UTV Iraq and al-Fallujah TV. Both sites are linked to the Iraqi politician and businessman Khamis al-Khanjar, who currently heads a Sunni Muslim parliamentary bloc; his son Sarmad is also involved in their operation. After the attack, Sabereen further claimed (without proof) that viruses had been added to the sites.
Part 2 of this analysis explores the attribution of each of the above cyberattacks to muqawama channels and platforms.